Patent Pipeline: Bitcoin Has Spurred Digital Currency Technologies
This patent covers high-end, cutting-edge technology that addresses the very real issue of hackers breaking into the blockchain and causing the digital currencies recorded there to no longer exist!
Testing transaction protocol to verify a device
Our fourth and newest property is U.S. Patent No. 9,735,958 for a “Key ceremony of a security system forming part of a host computer for cryptographic transactions.” This patent was published just last August, has just five Claims, and is assigned to Coinbase, Inc., a leading digital currency exchange. While the narrative of the Patent specifically references Bitcoins, the Claims are broadly written.
For digital currency trading firms, security is hyper-critical. This patent creates bundles for custodians of key data that are encrypted with the computer system’s custodians’ passphrases. Each bundle includes a master key share that is designed so it can also store an operational master key that is used for private key encryption during a checkout transaction and private key decryption when authorizing a payment. The bundles also include transport layer security keys for authenticating requests such as creating an application-programmable interface key for a web application so the system can be unfrozen after it has been frozen by an administrator.
If you cannot understand all of this, you definitely cannot hack into the system!
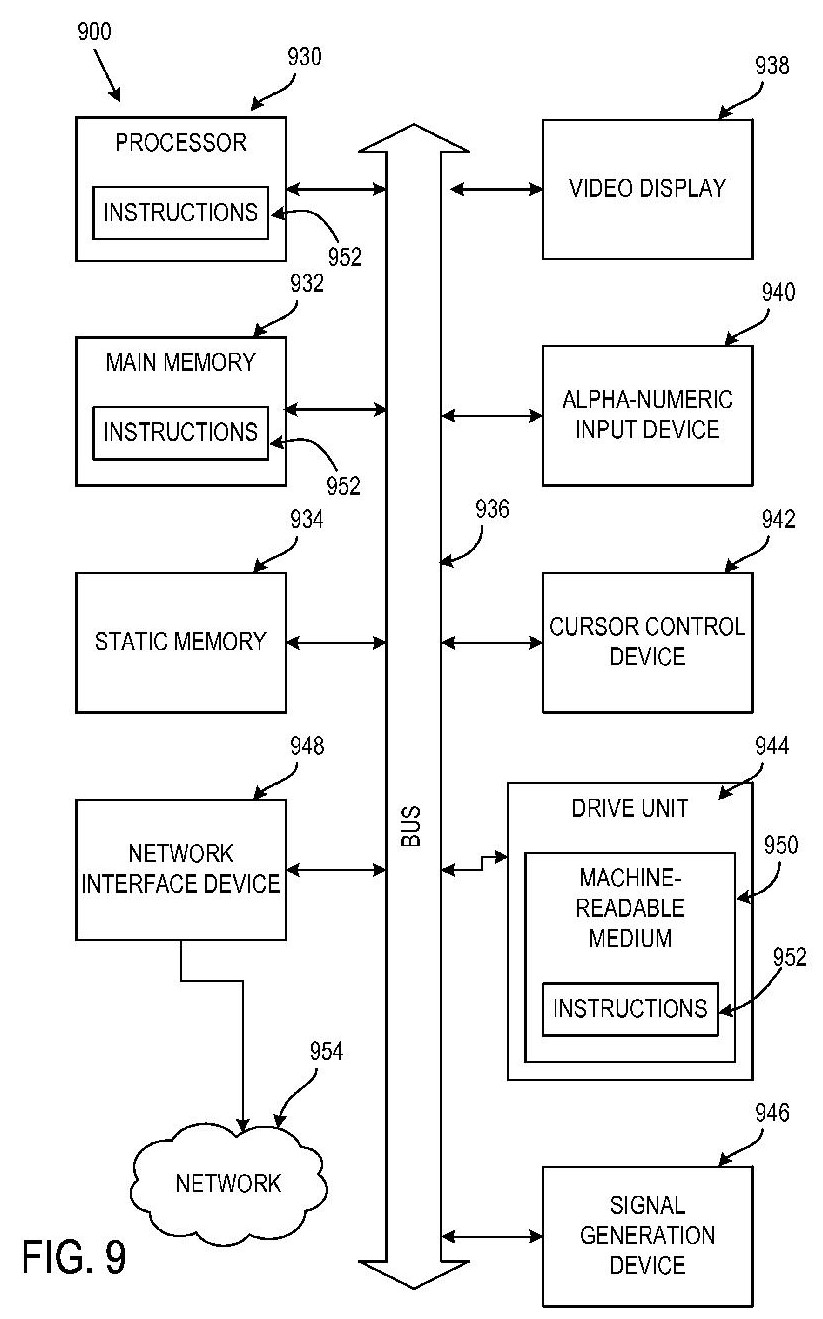
Figure 9 from U.S. Patent No. 9,735,958
is a block diagram of computer system that uses the cryptographic
technology covered by this patent.
A brave new world of technology challenges
We’ve come a long way from cashing our pay checks and buying groceries with paper money. The Bitcoin and its sister cryptocurrencies have virtually no physical characteristics! They only exist in a cyber-virtual reality. There are no hard-copy back-up files. Processing digital currency transactions, keeping those transactions safe and secure, and maintaining the blockchain to record those transactions safely from hackers or system failures will be an ongoing challenge requiring disruptive technologies.



















